September 2015
The lure of cloud is irresistible: Companies are drawn by the promise of new performance enhancements, infinitely scalable capacity, real cost savings, and business agility. But they struggle with how to apply all the various possibilities of cloud.
IT engineers and architects crafting their cloud blueprints face a multitude of decisions and no small amount of pressure: They need to choose among public, private, or hybrid cloud models—then determine whether software as a service (SaaS), infrastructure as a service (IaaS), platform as a service (PaaS), and other offerings are appropriate for their company's strategic and business direction.
There's no one-size-fits-all solution. How your enterprise can realize maximum returns from the growing potential of cloud is a nuanced, contextual question. It's a subject we'll be exploring in depth at the NetApp Insight™ event in October.
Looking Across the Data Lifecycle
An actionable cloud strategy starts with an understanding of data fabric and how it ties in with the evolution of data over its lifecycle. Data fabric makes IT systems work together, seamlessly connecting different data management environments across diverse clouds into a cohesive, integrated whole. (See the sidebar, "Understanding Data Fabric," for more information.)
Data fabric is the pane through which we want to manage our data across its lifecycle and the evolution of its lifecycle over time—irrespective of where it needs to live—from direct-attached storage through shared services to internal private cloud with secure multi-tenancy all the way to a hyperscale environment.
Data and the management of that data will evolve across time. Where that data will live and how companies exploit it will evolve over time as well.
Risky Business
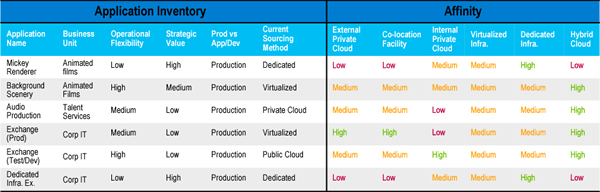
To help companies make sense of their data storage challenges and opportunities, we lead them through an Enterprise Transformation Workshop (ETW) for Cloud. The output of these one- to two-day sessions is a cloud-sourcing strategy. It starts with a risk-weighted analysis of their portfolio of business applications to help us understand what makes sense to move to the cloud or to a near-cloud environment, and what should not move out of house.
Risk, as defined in ISO 31000, refers to the effect of uncertainty on an organization's objectives. We evaluate a company's risk position against 39 different, interdependent variables, including legal risk, reputational risk, regulatory risk, operational risk, elements of stability and security, and so on.
This comprehensive analysis produces a detailed heat map that helps IT leaders understand whether a particular application would be better delivered in IaaS, PaaS, or SaaS; whether it would be better delivered via direct-attached, shared services, private cloud, hybrid cloud, public cloud—or combinations of these options.
Figure 1) The heat map helps companies understand their data storage options in light of the different aspects of risk they face.
Source: NetApp, 2015
The Roles of Risk
Risk unidentified is the highest risk of all. It's therefore essential to identify the different areas of risk within an organization—legal, operational, financial, reputational, security, and so forth—and the portfolio of applications that support the business value. Developing a durable cloud strategy means working closely with the corporate risk-management team.
We tie these findings back to criticality with the business, aligning each business application to the most appropriate delivery model—private, public, hybrid, or on premises—for the company's business demands.
The importance of this last step is impossible to overstate. It's surprising how many firms lack a clear, crisp definition of criticality that is aligned to their business value —they also haven't aligned that criticality to the actual applications and business processes they support.
By properly aligning risk, establishing use cases for the cloud, and identifying business needs, companies can improve their operational capabilities and drive their business objectives. At the end of the engagement, we present a list of actionable recommendations for successfully moving applications to the cloud.
Achieving Real Value
Risk management's objective is to that assure uncertainty does not negatively impact the business goals. Yet, in virtually any enterprise today, risk management is not an integral part of normal business or IT operations.
Our focus is to help companies understand how to translate risk management into a data management program. We realize that companies deal with two moving streams over time: the ongoing evolution of both risk and technology. It's important that someone in IT delivery focus on aligning changing business risk with business value over time, and how these variables impact the technology and how they use it.
Our engagement helps companies understand how to bring these two elements together, creating a blended view that leads to reduced risk and better-informed decisions.
Learning to Fish
Once we've conducted a cloud strategy development engagement with a company—including live working sessions, reviews, and assessments across IT and associated business units—we're always available to go back and revisit it with them. But we rarely need to. Because once we help them understand the process and go through it, we've in effect taught them to fish: they know how to integrate the capability within their operations.
Central to the recommendations we deliver at the end of a workshop is an identification of inflection points in business risk over time. Companies can always refer to this document, revisit their thought process, and cycle through it as business conditions and demands change.
It's our goal to help companies identify areas where they can achieve immediate value via incremental changes that meet business requirements in short time frames. This transformational approach enables a new level of alignment between business executives and IT management. Bringing these roles together to assemble a comprehensive cloud strategy helps drive better decisions and outcomes across the organization.
Learn More at Insight
NetApp Insight is our annual technical conference for storage and data management professionals. Held this year on October 12–15 in Las Vegas and November 16–19 in Berlin, Insight gives customers, engineers, consultants, and partners a forum for learning from industry experts and from each other.
We'll be talking about how organizations can develop a comprehensive cloud strategy that helps them drive maximum value over the lifecycle of their data. Register now to reserve your space in the sessions that matter most to your company.