Tech ONTAP Blogs
- Home
- :
- Blogs
- :
- Tech ONTAP Blogs
- :
- BlueXP Backup and Recovery Feature Blog: January '23 Updates
Tech ONTAP Blogs
BlueXP Backup and Recovery Feature Blog: January '23 Updates
- Archival Tier support for StorageGRID on On-Premise Connector to AWS Archive
- Support for GCP Customer-managed encryption keys (CMEK)
- Exporting Job Monitoring Report
Archival Tier support for StorageGRID on On-Premise Connector to AWS Archive
With the January release, BlueXP Backup and Recovery service has added support for Archive Tiers for StorageGRID for On-premise BlueXP Connector installations. With this new feature, customers can back up their data to the StorageGRID bucket and then move the data to any of the cloud service provider archive tiers of their choice. This feature is supported on ONTAP version 9.12.1 and above, and StorageGRID versions 11.3 and above. Currently, support only for archiving to AWS archive storage classes is available. Archiving to Azure and Google will be supported in the future releases.
How does Archival tier support for StorageGRID work?
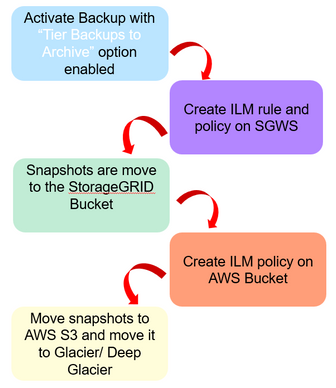
To tier the data from StorageGRID bucket to AWS archive tier, make sure that a volume is backed up with a policy that has the “Tier Backups to Archive” option enabled and the appropriate parameters set. This will make sure that ILM policy and rules are created on the StorageGRID and AWS to move the data from the StorageGRID bucket to AWS S3 bucket and from there to AWS Glacier or Deep Glacier archive tier when the archive after-days criteria are met.
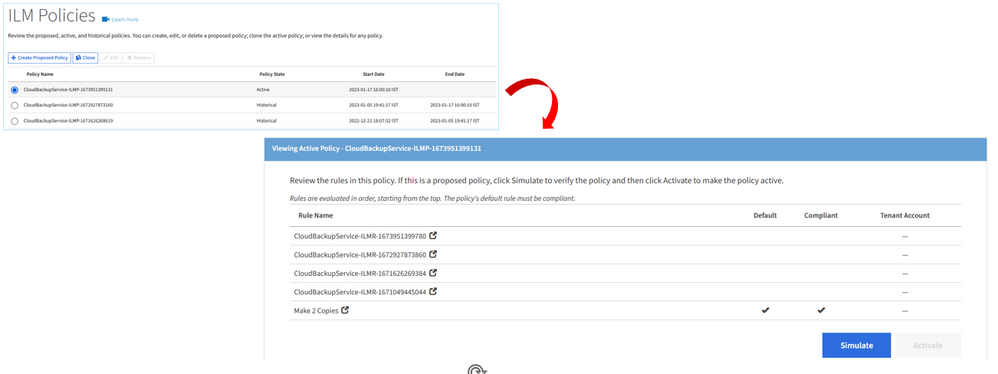
The following picture illustrates the StorageGrid ILM policy that will be created
A Cloud Storage Pool with the AWS S3 account will be created in StorageGRID to make sure that the snapshot objects are moved to archive. The rule will be also be created and updated in the StorageGRID ILM Policy. StorageGRID should have full control access to the bucket (s3:*). However , if this is not possible, the following permission should be granted to the StorageGRID.
- s3.AbortMultipartUpload
- s3:DeleteObject
- s3:GetObject
- s3:ListBucket
- s3:ListBucketMultipartUploads
- s3:ListMultipartUploadParts
- s3:PutObjects
- s3:RestoreObject
Please note the following while creating ILM rules on StorageGRID:-
a. If there is an existing ILM policy in the “proposed “state, the creation and activation of a new ILM policy will not be possible.
b. If there is an existing active ILM Policy, new rules will be added to the ILM policy to move the data to the archive tier.
c. If there are no ILM policies available, a new ILM policy with the relevant rule will be created and activated.
The following picture illustrates the ILM policiy that will created on the AWS S3 bucket
Enabling Archive Tier for StorageGRID
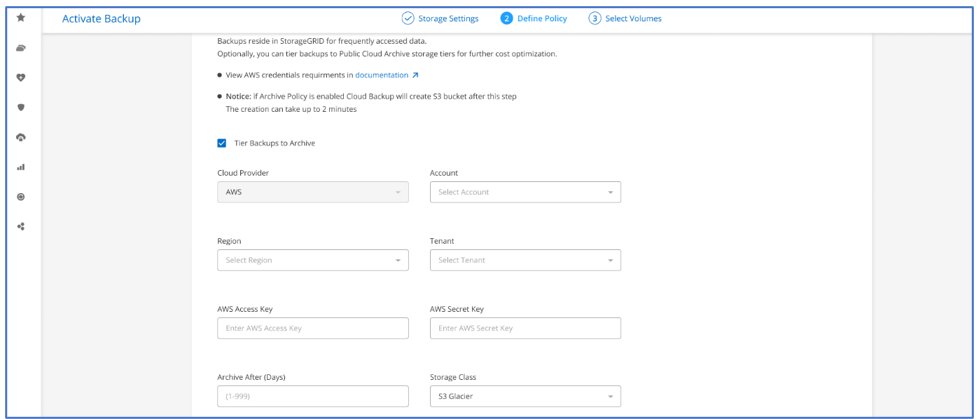
While enabling backup for a Working Environment on to StorageGRID bucket using the “Activate Backup” wizard, make sure to select the “Tier Backups to Archive” option under the “Define Policy” page . Choose the appropriate Cloud Provider. As mentioned before only AWS is supported with this release. Choose the required Account, Region, AWS Access Keys, AWS Secret Keys. Give in the number of days after which you would like to Archive in the “Archive After (Days)” and mention the Archive Storage Class that you like to set. Continue with the wizard and choose the required volume to be backed up and activate the backup. You can also enable backup to Archive Tiers on policies which already exists.
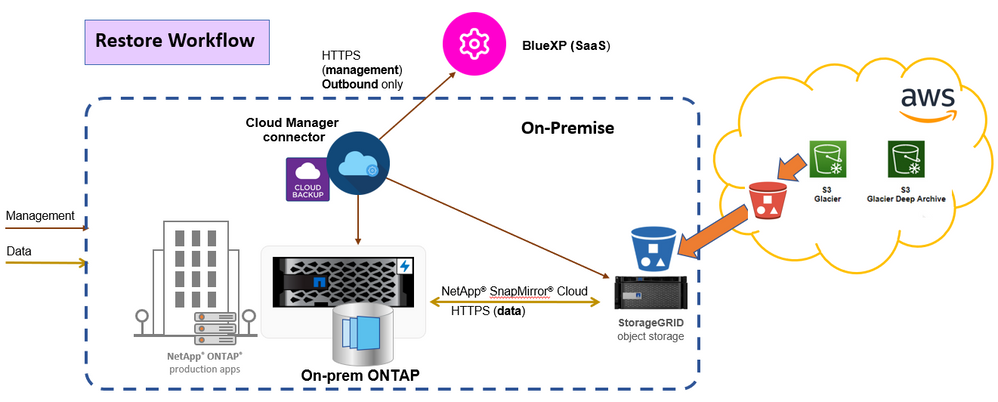
Restoring from Archive
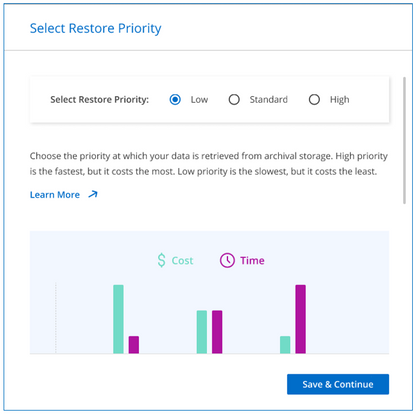
You can initiate the volume, folder or file restores from archive tier from the “Restore” dashboard. The request to restore with archive-retrieval-priority will be sent to ONTAP. ONTAP will now check for cloud objects available in the StorageGRID S3 bucket . If the backup objects are present in the StorageGRID S3 bucket, it will initiate a restore from bucket or else if the cloud backup has been archived, it initiates the archive re-hydration process which will pull the object from the AWS Archive tier to the Standard AWS S3 storage and then to StorageGRID S3 bucket. Once the object is hydrated back into StorageGRID S3 bucket, SnapMirror restore will be initiated after the approx. retrieval time based on the restore priority used.
You can restore volume , folder or files from the archive tier using the “Browse and Restore” tab or the “Search and Restore” tab in the “Restore” dashboard. Now to do the restore, select the source, choose the appropriate Working Environment and then the volume. Now all the snapshots pertaining to the volume will be listed. Choose the appropriate cloud backup to restore and click on continue. Now a “Select Restore Priority” window will be shown where the user can select the required restore priority. Now , proceed to select the destination , where you would like to restore and click on "Restore" to complete the process.
Support for GCP Customer-managed encryption keys (CMEK)
With the January release, BlueXP Backup and Recovery service for Google Cloud now supports using Customer-managed encryption keys while activating volume backups to the cloud. Customers can now encrypt storage buckets with their own managed keys along with Google-managed keys. Customer-managed encryption keys are encryption keys that you manage using Cloud KMS. This functionality lets you have greater control over the keys used to encrypt data at rest within supported Google Cloud services.
How do I create a CMEK?
You would need to follow steps similar to the following:-
1. Firstly, create a Cloud KMS key ring or choose an existing key ring. When creating your key ring, choose a location that is the same as the storage bucket.
2. Now, create or import a Cloud KMS key in the chosen key ring. This key is the CMEK key.
Please note the following:-
a. Both HSM (Hardware-backed) and Software generated keys are supported.
b. Both newly created or imported Cloud KMS keys are supported.
c. Only regional keys are supported, global keys are not supported.
d. Currently, only the “Symmetric encrypt/decrypt” purpose is supported.
e. The service agent associated with the Storage Account is assigned the “CryptoKey Encrypter/Decrypter (roles/cloudkms.cryptoKeyEncrypterDecrypter)” IAM role by the BlueXP Backup and Recovery service.
What are the permissions I need to give the BlueXP connector?
We would need to give the following permissions to the Storage Account attached to the BlueXP connector to make sure that we can use the Customer-Managed encryption keys.
a. cloudkms.cryptoKeys.get
b. cloudkms.cryptoKeys.getIamPolicy
c. cloudkms.cryptoKeys.list
d. cloudkms.cryptoKeys.setIamPolicy
e. cloudkms.keyRings.get
f. cloudkms.keyRings.getIamPolicy
g. cloudkms.keyRings.list
h. cloudkms.keyRings.setIamPolicy
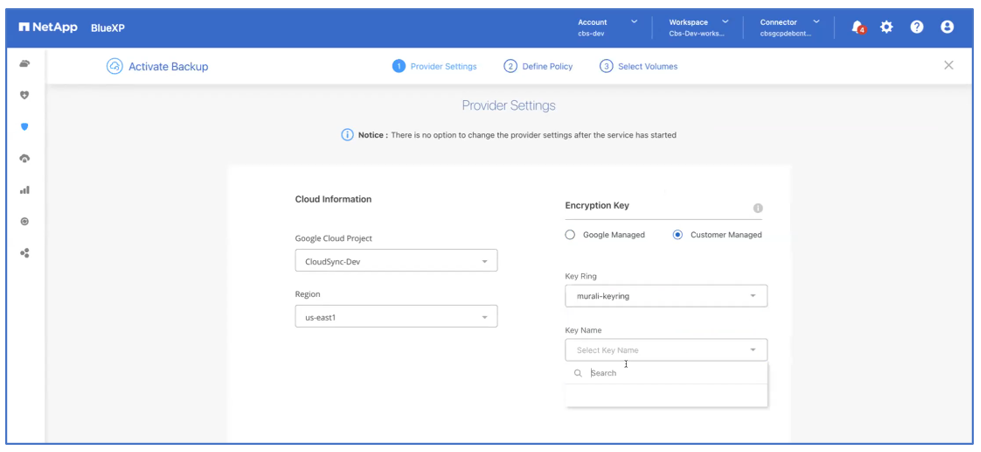
How do I Use the CMEK for Activating my Backup?
In the “Activate Backup” wizard, under the “Provider Settings” page, along with the “Google Cloud Project” and the “Region”, new options have been provided for selecting Google Managed encryption keys or Customer Managed encryption keys. Before selecting “Customer Managed”, make sure that the Customer Managed encryption keys are created before proceeding to activate the backup on the Working Environment. Also, make sure that the Customer Managed encryption keys are created in the same region in which the bucket exists.
Once the user selects “Customer Managed" encryption keys, options to enter the “Key Ring” and the “Key Name” will be displayed. Please note that the option to enable “Customer Managed" encryption keys on BlueXP Backup and Recovery UI is only available at the time of backup activation.
Exporting Job Monitoring Report
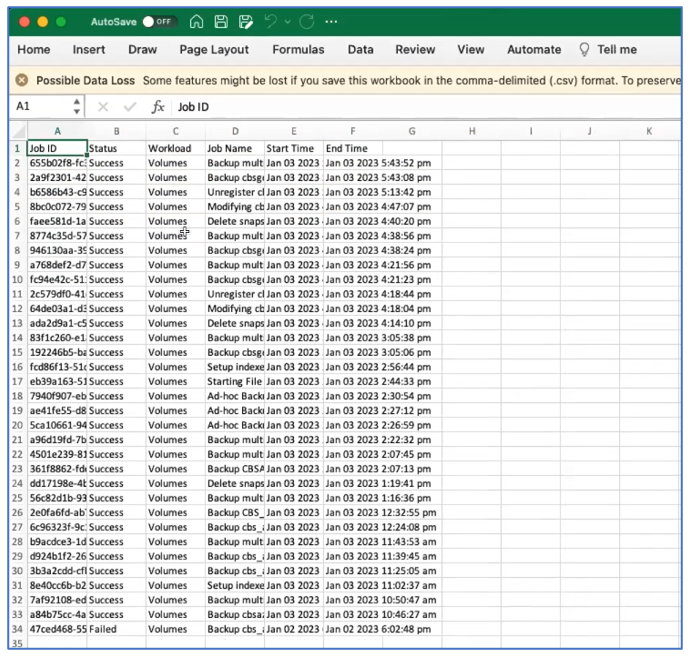
In this release, you can now download the Job Monitoring report based on the filter that you set for audit purposes. In the Job Monitoring UI, a download icon has been provided to download the report. You can set the filter to last 24 hours, last 12 hours, last 48 hours, last week, and last month and generate the report accordingly. If the filter returns no jobs to download, the download button will be disabled. At a time, It's possible to download 10K records using the download button.
The report will be generated in CSV format. All the columns selected will be downloaded in the generated CSV report. The following image shows a sample of the generated CSV job monitoring report.