Tech ONTAP Blogs
- Home
- :
- Blogs
- :
- Tech ONTAP Blogs
- :
- Cloud Backup: DataLock and Ransomware Protection Support
Tech ONTAP Blogs
Cloud Backup: DataLock and Ransomware Protection Support
- Introduction
- Scope of Cloud Backup DataLock and Ransomware Protection
- How do I enable DataLock and Ransomware Protection?
- Permission Required for DataLock and Ransomware protection
- Creating Governance and Compliance Policies
- How does Cloud Backup DataLock Work?
- How does Ransomware Protection Work?
- Understanding the UI for DataLock and Ransomware Protection
- Let us know…
Introduction
Organizations continue to face the challenge of ransomware and attacks can cost a business time, resources, and reputation. An organization typically has two options after it has encountered ransomware: pay the ransom or restore from backups. Protection against ransomware attacks has become one of the high-priority requirements among customers.
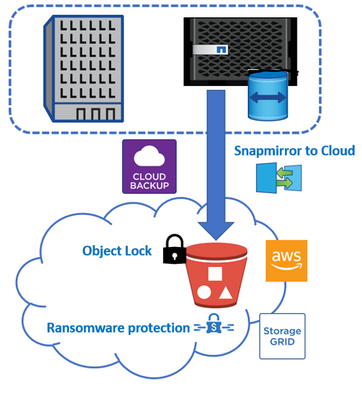
Cloud Backup has now introduced support for DataLock and Ransomware protection on Cloud Snapshots. With this feature, Cloud Backup provides a mechanism to lock the Cloud Snapshots replicated via SM-C and provides the ability to detect a ransomware attack and recover a consistent copy of the cloud snapshot. The solution uses both SM-C and ADC to achieve the above functionality. Currently, the feature is supported only for StorageGRID and AWS.
Scope of Cloud Backup DataLock and Ransomware Protection
- Supported sources: On-prem and CVO, minimum ONTAP version 9.11.1
- Supported destination: AWS S3, StorageGRID, Azure and GCP (around Dec 2022)
- Supported deployment: SaaS & Dark-Site (on-prem dark site with StorageGrid)
- Applicable only for new backup activation (not applicable on existing backup copies)
- No interoperability with archival policy
How do I enable DataLock and Ransomware Protection?
To enable DataLock and Ransomware Protection, we have to choose the appropriate mode “Governance or Compliance” under the “DataLock and Ransomware Protection” section of the “Define Policy” UI of the “Activate Backup for Working Environment” wizard as shown below.
- If you choose the “Governance” mode, users with specific permission can overwrite or delete protected backup files during the retention period. However, for ”Compliance” mode no users can overwrite or delete protected backup files during the retention period.
Important:-
- Make sure that the “DataLock and Ransomware Protection” is set while enabling the Cloud Backup service on the Working Environments.
- Please note that if you miss setting the “DataLock and Ransomware Protection” while enabling the Cloud Backup service on the Working Environments, you will not be able to enable the feature thereafter.
- DataLock protection mode (Governance and Compliance) cannot be changed after the policy is created.
- Disabling or modifying DataLock and Ransomware Protection feature is not possible.
When “DataLock and Ransomware Protection” is enabled, the cloud bucket that will be provisioned as a part of the backup activation process will have object locking enabled. It will also have Auto-purging of non-current versions on the bucket will be enabled and set to 1 day.
Permission Required for DataLock and Ransomware protection
To enable DataLock and Ransomware on AWS S3, make sure the following permissions are available
- "s3:GetObjectVersionTagging",
- "s3:GetBucketObjectLockConfiguration",
- "s3:GetObjectVersionAcl",
- "s3:PutObjectTagging",
- "s3:DeleteObject",
- "s3:DeleteObjectTagging",
- "s3:GetObjectRetention",
- "s3:DeleteObjectVersionTagging",
- "s3:PutObject",
- "s3:GetObject",
- "s3:PutBucketObjectLockConfiguration",
- "s3:GetLifecycleConfiguration",
- "s3:ListBucketByTags",
- "s3:GetBucketTagging",
- "s3:DeleteObjectVersion",
- "s3:ListBucketVersions",
- "s3:ListBucket",
- "s3:PutBucketTagging",
- "s3:GetObjectTagging",
- "s3:PutBucketVersioning",
- "s3:PutObjectVersionTagging",
- "s3:GetBucketVersioning",
- "s3:GetBucketAcl",
- "s3:BypassGovernanceRetention",
- "s3:PutObjectRetention",
- "s3:GetBucketLocation",
- "s3:GetObjectVersion"
Creating Governance and Compliance Policies
In this section, we will discuss Cloud backup policy behavior when Cloud Backup is enabled with a Governance or Compliance policy in the Working Environment.
- If the policy used while enabling Cloud backup on the Working Environment is a Governance or Compliance policy, you cannot create normal policies thereafter.
- If the volume is assigned a Governance policy, it cannot be changed to a normal policy.
- If the volume is assigned a Compliance policy, it cannot be changed to a normal policy.
- If the volume is assigned a normal policy, it cannot be changed to Governance or Compliance policy as the DataLock and Ransomware Protection feature cannot be enabled on an already CBS-enabled Working Environment.
- If the initial policy is a Governance policy, you can create different Governance policies and change the volume to a different Governance policy. Please note that you will not be able to create a Compliance enabled Policy.
- If the initial policy is a Compliance policy, you can create a different Compliance policy and change the volume to a different Compliance policy. Please note that you will not be able to create a Governance enabled Policy.
How does Cloud Backup DataLock Work?
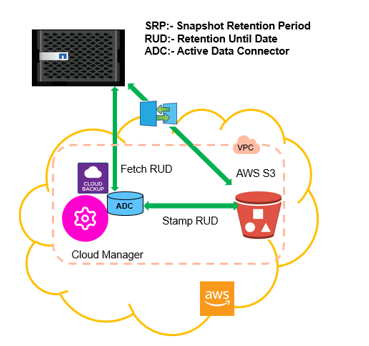
To lock an object, cloud providers provide a way to set the ‘Retention Until Date’ (RUD which is calculated based on the Snapshot Retention Period) in the object metadata during which the object version cannot be deleted or overwritten.
What is Snapshot Retention Period (SRP) and how is it calculated?
When “DataLock and Ransomware Protection” is enabled through the Cloud Backup policy, the Snapshot Retention Period’(SRP) is calculated as per the label and retention count defined by the user in the Cloud Backup policy.
The minimum SRP that will be assigned would be 30 days.
Let's try to understand how the Snapshot Retention Period (SRP) is calculated:
- If the user chooses the Daily label with Retention Count 20 ( The SRP is 20 days which defaults to 30 days.)
- If the user chooses the Weekly label with Retention Count 4 (The SRP is 28 days which defaults to 30 days.)
- If the user chooses the Monthly label with Retention Count 3 (The SRP is 90 days)
- If the user chooses the Yearly label with Retention Count 1 (The SRP is 365 days)
DataLock on an object is set by applying a retention period to an object version explicitly by specifying a “Retain Until Date or RUD” for the object version. Amazon S3 stores the Retain Until Date setting in the object version's metadata and protects the object version until the retention period expires.
What is Retention Until Date (RUD) and how is it calculated?
- The 'Retention Until Date' (RUD) is computed based on the SRP which is recorded in the metadata of the object while transferring using SM-C.
- The 'Retention Until Date’ (RUD) is calculated by summing the SRP and the Buffer.
- Buffer = Buffer for Transfer Time (6 days) + Buffer for Cost Optimization (8 days). Buffer is set as 14 days.
- Minimum RUD will be 30 days + 14 days
Example:-
- If you create a Monthly backup schedule with 12 retentions, your backups are locked for 12 months (plus 14 days) before they are deleted (replaced by the next backup file).
- If you create a backup policy that creates 30 daily, 7 weekly, 12 monthly backups there will be three locked retention periods. The "30 daily" backups would be retained for 44 days (30 days plus 14 days buffer), the "7 weekly" backups would be retained for 9 weeks (7 weeks plus 14 days), and the "12 monthly" backups would be retained for 12 months (plus 14 days).
- If you create an Hourly backup schedule with 24 retentions, you’d think that Backups are locked for 24 hours. However, since that is less than the minimum of 30 days, each backup will be locked and retained for 44 days (30 days plus 14 days buffer).
Please Note:-
- Be aware that old backups are deleted after the DataLock Retention Period expires, not after the backup policy retention period.
- The DataLock retention setting overrides the policy retention setting from your backup policy. This could affect your storage costs as your backup files will be saved in the object store for a longer period of time.
How do we set Retention Until Date (RUD) on the cloud backups?
- Cloud Backup uses the snapshot list REST API in Active Data Connector (ADC) to determine all the snapshots that are yet to be locked based on the SnapMirror Policy.
- For each of these snapshots, it uses ADC to stamp the RUD in all the objects belonging to the snapshot. This guarantees that the snapshot is locked until the RUD expires.
How does Ransomware Protection Work?
Ransomware Scan
In this section, we will examine how Ransomware detection scans are run by Cloud Backup. As soon as you enable Cloud Backup in the Working environment and configure "DataLock and Ransomware Protection," the ransomware scans are initiated. The Ransomeware scans are run in the below-mentioned scenarios.
- The scans on the cloud backup objects are initiated soon after they are transferred to the cloud object store. The scan is not performed on the backup file when it is first written to cloud storage, but when the next backup file is written
- The Ransomware Scans can be initiated when the backup is selected for the restore process.
- The scan can also be done on-demand as required by the user.
How does the scan work?
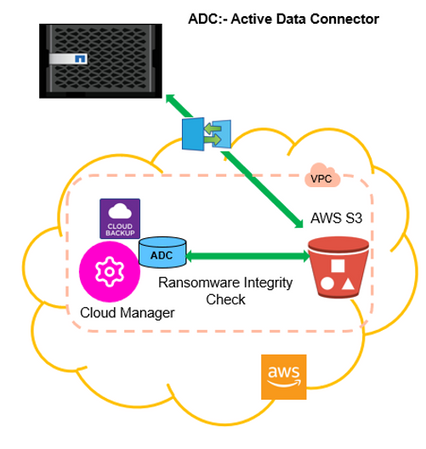
Now let's try to understand how the Ransomware scans work.
- Before the Ransomware scans are initiated, Cloud Backup checks to make sure that the snapshot is stamped.
- Cloud backup employs the Active Data Connector Integrity Checker REST API to start Ransomware scanning as necessary.
- The detection of ransomware attacks is performed using checksum comparison.
- The Active Data Connector Integrity Checker REST API triggers a Ransomware scan of the cloud backup objects on the cloud object store by verifying the checksum of the different backup object versions.
- Based on the result of the scan Cloud Backup initiates the recovery process.
Snapshots can be scanned on an on-demand basis for any ransomware attacks if necessary.
How does the Recovery process work?
When a Ransomware attack is detected, Cloud Backup uses the Active Data Connector Integrity Checker REST API to start the recovery process. The oldest version of the data objects is the source of truth and is made into the current version as part of the recovery process.
Let's see how this works:-
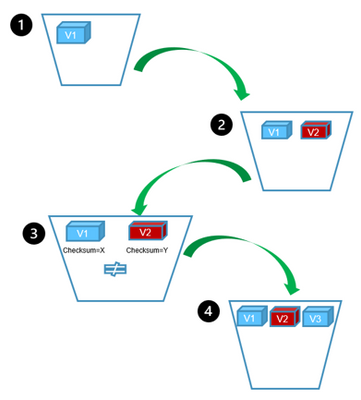
- In the event of a ransomware attack, the Ransomware tries to overwrite/ delete the object in the bucket.
- Since the AWS S3 buckets are versioning-enabled it automatically creates a new version of the backup object. If an object is deleted with versioning turned on, it is only marked as deleted but is still retrievable. If an object is overwritten, previous versions are stored and marked.
- When a Ransomware scan is initiated, the checksums are computed for both object versions and compared, If the checksums are inconsistent, potential ransomware has been detected.
- The recovery process involves reverting to the last known good copy. V3 is created (duplication of V1)
Please Note:-
• DataLock and Ransomware Protection feature scans only cloud backups. It does not support scanning local snapshots, Ransomware attacks on local snapshots cannot be detected.
Understanding the UI for DataLock and Ransomware Protection
In this section, we will look into the various Cloud Backup UI changes that were introduced to show the status and results of the DataLock and Ransomware Scan run on the cloud backups stored in the Cloud object store
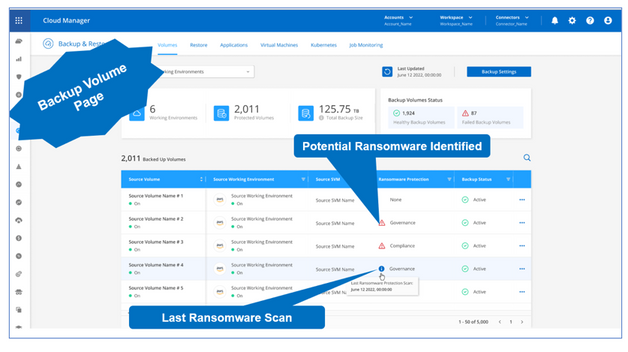
Backup Volume Page
A new “Ransomware Scan” column has been introduced on the Backup Volume Page. It displays the different status of the Ransomware scans on a Volume level like potential ransomware identified, tool-tip showing the last scan time, and successful ransomware scan with scan time.
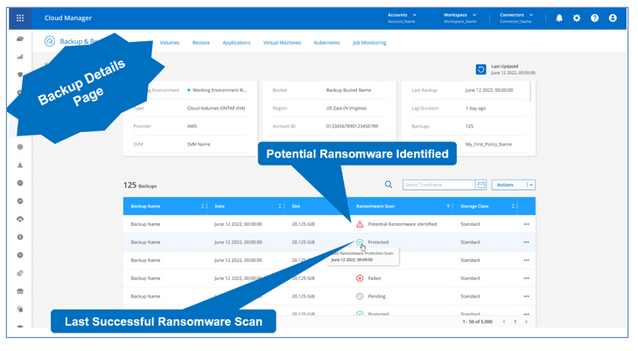
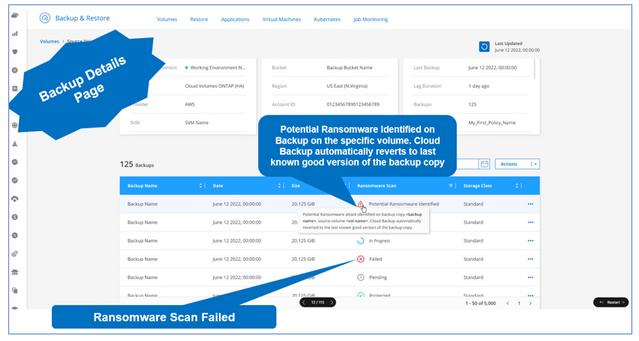
Backup Details Page
A new “Ransomware Scan” column has been introduced on the Backup Details Page. It displays the different status of the Ransomware scans on the backup level like potential ransomware identified, tool-tip showing the last scan time, ransomware scan failure with scan time, and successful ransomware scan with scan time.
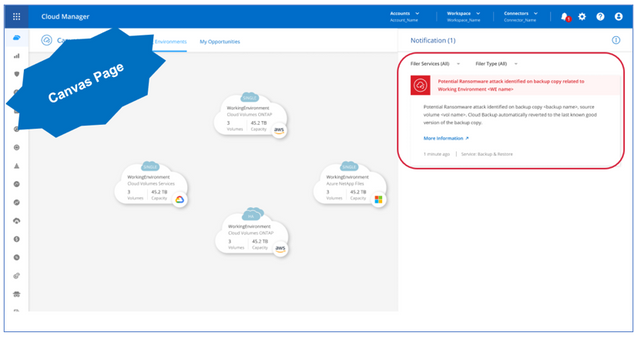
Canvas Page
Notifications have been included on the Canvas Page which notifies that a potential ransomware attack has been identified on a backup copy of a specific volume related to a specific Working Environment.
Notifications have been included on the Canvas Page which notifies that a potential ransomware attack has been identified on a backup copy during the restore of a specific volume related to a specific Working Environment. It will also highlight that Cloud Backup reverted to the last good known version of the backup copy.
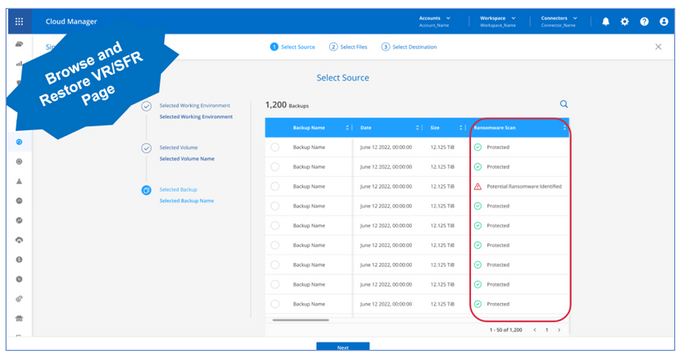
Browse and Restore Pages
A new “Ransomware Scan ” column has been introduced on the Selected Backup Details Page. It displays the different status of the Ransomware scans on the backup level like potential ransomware identified, tool-tip showing the last scan time, ransomware scan failure with scan time, and successful ransomware scan with the scan time.
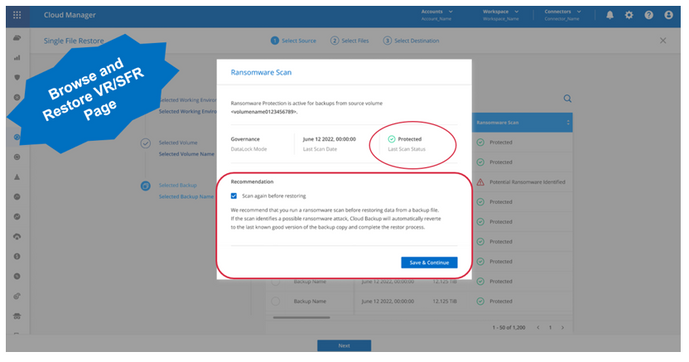
Browse and Restore Pages – Restore Message
A “Ransomware Scan” UI will be shown upon selecting a snapshot to restore the backup. This restore confirmation message shows the details of the DataLock mode, and last run scan time information and also includes a recommendation to run a ransomware scan before proceeding with the scan. This is an optional scan, the user can uncheck to skip the ransomware scan.
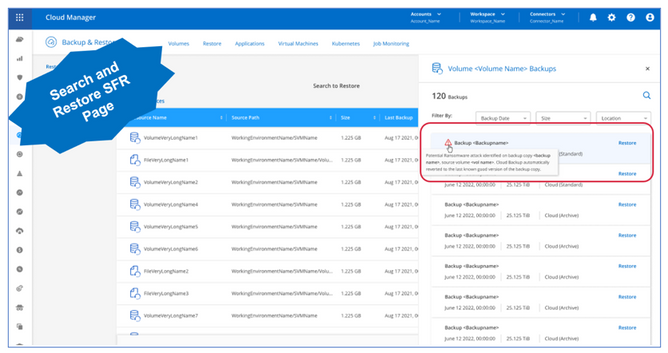
Search and Restore Page
More details about the ransomware scan have been provided on the “Backup Details” right navigation pane UI. It displays the different status of the ransomware scans on the backup level like potential ransomware identified, tool-tip showing the last scan time, ransomware scan failure with scan time, and successful ransomware scan with the scan time
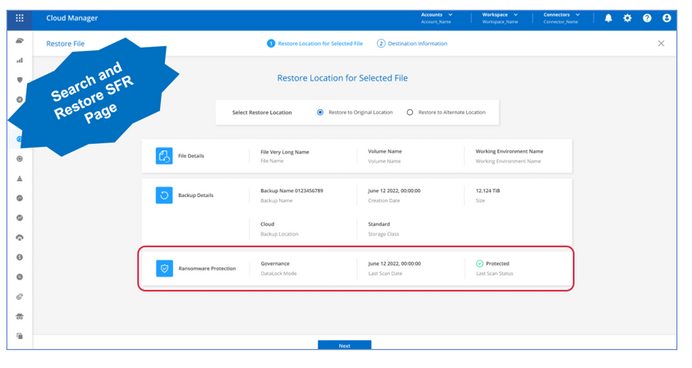
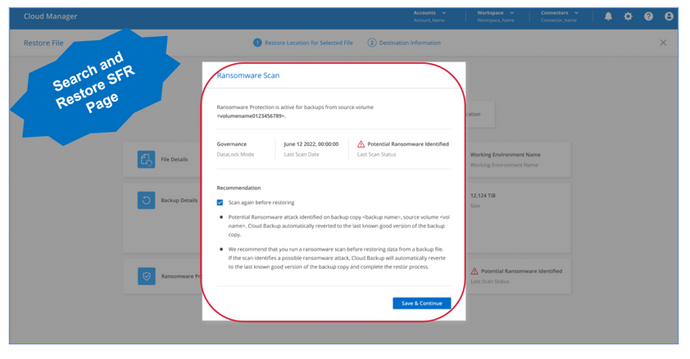
Search and Restore Page- Restore UI
The “Restore Location for Selected File” UI under the Search and Restore feature, also now display the information of the backup DataLock Mode and the status of the ransomware scan run.
Clicking the “Next” button will bring up a “Ransomware Scan” UI, which displays the “DataLock” mode, the previous scan time, and the result of the ransomware scan. It also shows a recommendation to run a ransomware scan before proceeding with the restore process. This is an optional scan, the user can uncheck to skip the ransomware scan.
Let us know…
Please try it out and let us know. In this blog , we haven’t covered every possible scenario, and we know that you’ll have questions and concerns, so please contact us on Teams Group.